A single compromised password was reportedly responsible for the Colonial Pipeline ransomware attack that triggered fuel shortages in Eastern states in May last year. That same month, a foreign government agent breached the Alaska Department of Health and Social Services website, an attack that affected services for weeks and is still being investigated. Then in October, Russia’s top intelligence agency attempted to get at U.S. government and corporate data stored in the cloud—just months after the White House sanctioned Moscow for its role in previous hacks, including SolarWinds, which infiltrated numerous federal agencies.
All 50 states faced cyberattacks against public infrastructure in the past 24 months, with new reports of state and local government incidents being added weekly. Nationwide, hardening cybersecurity has taken on a renewed sense of urgency.
At least 45 states and Puerto Rico introduced or considered more than 250 bills or resolutions last year dealing significantly with cybersecurity. A few of the enacted bills provide a snapshot of the innovative ways legislators are strengthening the security of government computer systems.
An Intractable Problem
Constant cyberattacks originating from foreign countries or on behalf of foreign governments, along with increasingly sophisticated perpetrators, make it difficult for security professionals to stay a step ahead. Ransomware attacks, which often have devastating and costly consequences, were the most common type of cyberattack on government organizations in 2020, according to IBM’s X-Force Threat Intelligence Index 2021.
The COVID-19 pandemic only exacerbated the problem, causing disruption and shifts in the way governments operate, and creating additional cybersecurity risks due to a sudden move to a remote workforce. Criminals also took advantage of people’s fears during the crisis by launching social engineering attacks to manipulate individuals into giving up personal information or allowing access to networks.
Government IT professionals and the IT industry have expertise and tools to monitor and protect against attacks, but tackling the problem takes much more than that. Some of the challenges include:
- Sophisticated organized crime gangs working on behalf of foreign governments.
- Maintaining and securing outdated legacy IT systems.
- Recruiting and retaining highly skilled cybersecurity professionals.
- Maintaining and securing the large collections of sensitive and personal data held by government agencies.
- The difficulty of tracking ransomware payments made with Bitcoin and other cryptocurrencies.
- Obtaining evidence or protecting the chain of custody of evidence.
- Jurisdictional limitations exposed by the involvement of many cross-border actors.
- Internet anonymity, making it difficult to attribute cybercrimes to specific actors.
Championing Cybersecurity Best Practices
For years, all 50 states have had computer crime laws in place to penalize hackers, and all states have some type of cybersecurity program in executive branch agencies.
More recently, legislatures have amended and passed new data security laws. A review of enacted state cybersecurity legislation in 2021, however, suggests that legislatures are now taking an even more active role in protecting government resources.
Some of the best practices legislatures are endorsing include strengthening governance; mandating training and adherence to established security standards; requiring incidence response programs and reporting; and recognizing the need to update legacy systems and IT infrastructure.
Strengthening Governance
“We’re living in a time of historic cybersecurity threats … and it’s time for us to have a stronger governance structure; it’s time for us to get more serious about what evidence-based best practices look like,” Washington Sen. Reuven Carlyle (D) said during a Senate committee hearing in early 2021. Carlyle’s legislation, effective last July, created an office of cybersecurity and set forth a detailed list of requirements for a centralized protocol to protect and manage state IT assets.
Colorado also passed legislation aimed at strengthening governance by broadening the powers of the Legislature’s Joint Technology Committee. The law also charges the Colorado Cybersecurity Council with developing a whole-of-state cybersecurity approach, including better coordination and setting of strategic statewide cybersecurity goals, road maps and best practices.
Minnesota lawmakers created a Legislative Commission on Cybersecurity to review cybersecurity policies and practices of state agencies and to recommend changes in policy to protect the state. Other legislative committees created expressly to deal with cybersecurity include those in the California Assembly and Senate, and joint committees in Louisiana and Massachusetts.
Several other legislatures have mandated statewide strategic plans for cybersecurity or created advisory bodies. Maryland now requires the Secretary of Information Technology to advise on and oversee a consistent cybersecurity strategy for state government. Nevada, Ohio and Vermont also require statewide strategic plans. Florida and New Hampshire created statewide cybersecurity advisory councils within their IT departments last year.
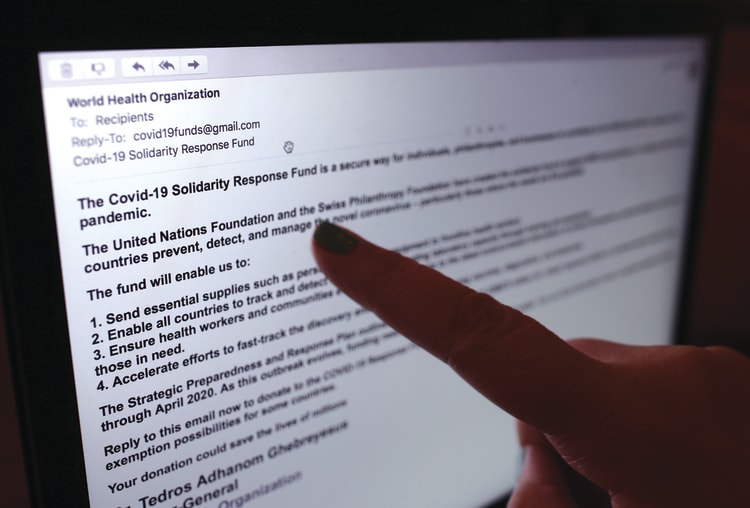 A phishing email from someone posing as the head of the World Health Organization asked recipients to donate money to a coronavirus fund. One study found that 90% of data breach incidents are caused by employees’ mistakes, such as clicking on a phishing email. Although many states offer cybersecurity training for employees, some lawmakers are mandating such programs. (Yui Mok/PA Images via Getty Images)
A phishing email from someone posing as the head of the World Health Organization asked recipients to donate money to a coronavirus fund. One study found that 90% of data breach incidents are caused by employees’ mistakes, such as clicking on a phishing email. Although many states offer cybersecurity training for employees, some lawmakers are mandating such programs. (Yui Mok/PA Images via Getty Images)
Adopting Security Measures and Standards
More than half the states already require that state government agencies have some type of data security measures to protect their information. Some, however, simply direct agencies to implement and maintain undefined “reasonable security measures” or to develop and update information security policies and guidelines. More recent state laws are more specific and require agencies to adopt standards, conduct risk assessments, undergo security audits or take other measures.
There are many different standards and certifications that offer guidance on various practices and controls necessary to achieve and maintain a level of security. Two of the most notable are from the National Institute of Standards and Technology, known as NIST, and the Center for Internet Security. NIST’s cybersecurity framework provides voluntary standards, guidelines and practices for organizations to follow to manage and reduce cybersecurity risk. The Center for Internet Security’s CIS Controls outline a prioritized set of actions that can help protect organizations from cyberattacks.
"Ensuring that your statutory requirements don’t become quickly outdated with the development of technology is critical." —California Assemblywoman Jacqui Irwin
California Assemblywoman Jacqui Irwin (D), co-chair of NCSL’s Cybersecurity Task Force, has sponsored several bills that require the adoption of the NIST security and privacy policies, standards and procedures. “They are the gold standard in cybersecurity, are continuously updated and provide alignment with federal agencies,” she says. Irwin has incorporated into legislation this year NIST standards that certain state agencies must use in adopting coordinated vulnerability disclosure programs and authorizing remote identity verification programs for vital records.
Irwin says that newly developed NIST standards can even bolster prior enacted legislation that relies on general terms like “reasonable,” as with her legislation enacted in 2018 requiring reasonable security for Internet of Things devices. “Ensuring that your statutory requirements don’t become quickly outdated with the development of technology is critical,” she says. Florida passed legislation in 2021 requiring state contracts for information technology to meet the NIST cybersecurity framework, and Nevada law currently requires government agencies that maintain records with personal information to comply with the CIS controls or the NIST standards.
Requiring Security Awareness Training
Many cybersecurity incidents and breaches are caused by individual error. One study found that 90% of data breach incidents are caused by employees’ mistakes, such as clicking on a phishing email. Although many states offer cybersecurity training for employees, some lawmakers are mandating such programs.
“Even some of the strongest security systems may be bypassed or compromised by employees,” Texas Rep. Giovanni Capriglione (R) says. He sponsored legislation enacted in 2018 requiring all state government employees to complete a certified cybersecurity training program. Capriglione sponsored additional legislation last year that strengthens and clarifies the requirements and adds certain elected and appointed officials to the list of those who must undergo training.
Virginia joined Texas in 2021 in requiring its state agencies to provide annual training for employees. The new Virginia law also requires the state CIO to develop a curriculum and materials for information security awareness training.
Improving Incident Response, Reporting and Collaboration
As government continues to be a target, there’s new emphasis on how to prepare for and manage responses to cybersecurity incidents or breaches. Another recent trend relates to the reporting of cybersecurity incidents to help identify the frequency and types of attacks.
Last year, lawmakers in Georgia, Indiana, North Dakota, Washington and West Virginia passed legislation requiring state agencies, and in some cases, local entities, to report cybersecurity incidents to a central state office. Louisiana now requires managed service providers doing business with the state to report any incidents and payments of ransom to the State Fusion Center, a threat-sharing clearinghouse.
The impetus to allow sharing of threat information in Georgia arose a few years ago when a local government association asked Rep. Don Parsons (R) to help localities respond to cyberattacks. “At that point, they had few resources,” Parsons says, but there were also few details about the problems localities faced. Parsons developed legislation to require local and state entities to report cyberattacks to the state’s director of emergency management and homeland security. “We have to know what’s going on before we know what we can do and how to help,” he says.
Parsons had concerns about utilities, so his bill requires them to report cyberattacks to the state energy department. The legislation also allows the governor to enter into agreements with state military commands to improve cybersecurity education and job placement opportunities for residents.
A new North Dakota law encourages collaboration among state, local, tribal and territorial governments by authorizing agreements that allow the entities to consult and share information about how to develop cybersecurity strategy, prevention efforts and response strategies.
Modernizing IT Systems and Improving Cybersecurity
Only half the states have a dedicated cybersecurity budget line item, and most state cybersecurity budgets are less than 3% of their overall IT budget—compared with an average of more than 10% in the private sector, according to NASCIO, the National Association of State CIOs. NASCIO encourages state governments to establish a dedicated budget line item for cybersecurity as a subset of the overall technology budget.
"Cybercriminals love outdated IT. Old IT costs more to maintain, makes it harder to attract IT professionals, and is an obstacle to improving web-based customer service for Texas residents and businesses." —Texas Rep. Giovanni Capriglione
The line item can give legislators more visibility into state cybersecurity expenses and can help identify funding gaps.
A new Texas law, also sponsored by Capriglione, creates a dedicated fund in the state treasury to be used to improve and modernize state agency information resources, including legacy system projects and cybersecurity projects. It also creates a committee to review investment and funding strategies for projects to improve or modernize state agency IT resources.
“Cybercriminals love outdated IT hardware, software and systems, and unfortunately our state government has plenty of costly old IT,” Capriglione says. “Old IT costs more to maintain, makes it harder to attract the next generation of state government IT professionals, and is an obstacle to improving web-based customer service for Texas residents and businesses.”